Welcome to the second article in our series of articles about container technologies in Fedora! This article will deal with Docker, a tool used to automate containerization of software using features of the Linux kernel.
What is Docker?
Docker is a high level set of tools that allows multiple isolated applications to run on a same host platform. Unlike other containerization software we talk about in this series, Docker is meant to run a system with a single process. In addition to providing these tools, Docker provides a “hub” for containers created by others.
Creating the container
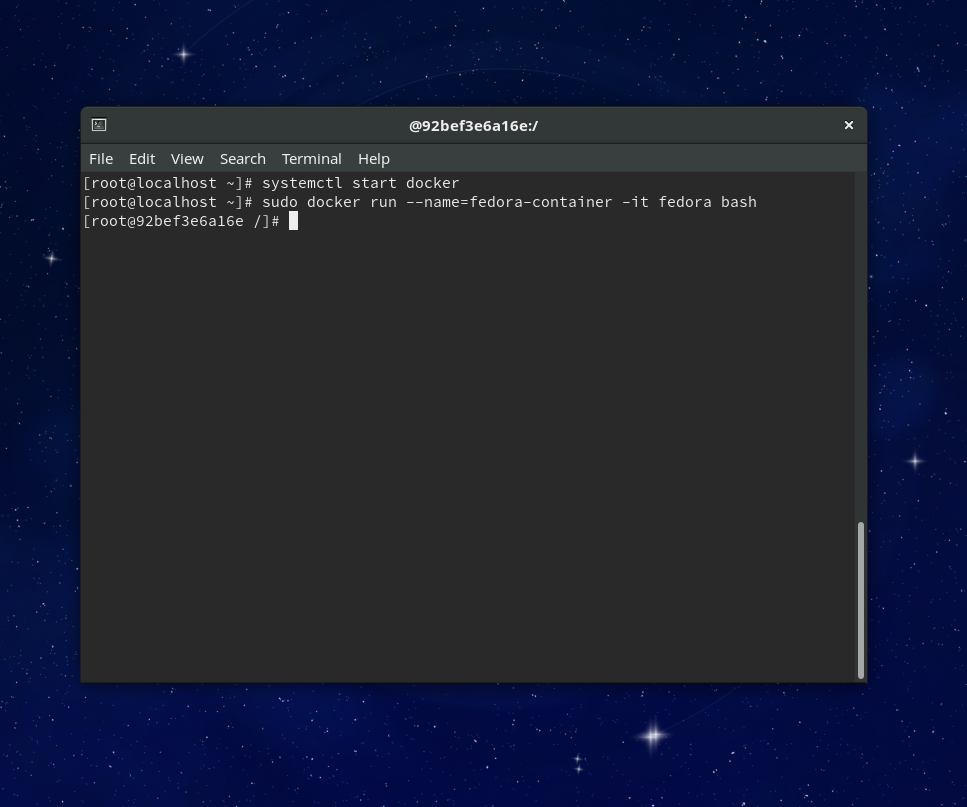
Creating a container with Docker is extremely easy. We will be using the Docker command line tool to set up a Fedora 24 container named “fedora-container”. You’ll need to install Docker, if you don’t already have it, with the usual sudo dnf install docker.
Before it is possible to run a container, you will need to start the Docker daemon. To do this, run systemctl start docker.service. You can then run a container for Fedora using the command sudo docker run –name=fedora-container -it fedora bash, which will download an image for a basic Fedora container from Docker Hub.
Using the container
Docker is designed to run one process per container, but you can run more if you want to. sudo docker exec -it fedora-container bash would run bash in your container alongside the process you had originally started. You can replace bash with any command you’d like to run in the container.
The network will already be available, and you can use it to install packages using the standard DNF commands. You can stop the container either by stopping the Docker daemon, with systemctl stop docker, or with docker stop fedora-container. You can then start the container again when you need it with docker start fedora-container. It is also possible to temporarily pause execution of a container, using docker pause fedora-container.
Particularly useful is the docker cp command, which you can use to copy files from and to the container. The command docker cp fedora-container:/root/source target will copy the file source from your home folder on the container to the name ‘target’ in the current folder, while docker cp source fedora-container:/root/target will copy in the reverse direction.
Dockerfiles
You can use images for other systems than Fedora by pulling images from the Docker Image Library. However, if you want to create and run applications or services using Docker, you will want to create your own images. Docker is able to create images automatically if you tell it how to in a Dockerfile. A Dockerfile contains the instructions and commands that will assemble the image you want to run in a container. The Dockerfile reference explains the format.
Fedora packages many example Dockerfiles that you can use to learn about Docker images and to create your own. You can install the Dockerfiles with sudo dnf install fedora-dockerfiles; they will be put in /usr/share/fedora-dockerfiles/. The Fedora Developer Portal has additional useful information about Docker in Fedora.




Michael Krumpe
I found that follwing these steps on a vanilla Fedora desktop install still needed appropriate permissions to be added, and would get a docker daemon error.
http://stackoverflow.com/questions/33562109/docker-command-cant-connect-to-docker-daemon
sudo groupadd docker
sudo gpasswd -a docker
sudo service docker restart
newgrp docker
Michal Srb
Using
should work just fine, this is worth reading: http://www.projectatomic.io/blog/2015/08/why-we-dont-let-non-root-users-run-docker-in-centos-fedora-or-rhel/
Ron Humble
I would like to see at least a link or a sentence regarding the security implications of Docker. I have not seen the first Docker article, perhaps this was covered. I am a total newbie with Docker and my comments may be pure ignorance.
Red Hat suggests not using “docker pull” as it downloads and installs in one step, executing unknown command (as root or user “docker”, I believe) on your machine. It is like inviting someone into your home and then going to sit in a closet while who knows what occurs. I have so far only downloaded the Fedora image and verified its checksum before installing.
A useful companion to an image repository, would be a vetted Dockerfile repository. A Dockerfile and Docker version used to create an image should be a part of every image. One should be able to download an image’s Dockerfile separate from the image. A centralized vetting and verification process, though challenging, would speed the adoption of container technology. Until I learn of some verification process, I will stick to building my own images.
Isaac
I have the exact same feeling. While container security is getting more attention recently, it still seems like it is not a first class citizen. Maybe that could be a topic for another Fedora Magazine article: “How to keep your containers up to date”.