A previous article discussed password management tools that use server-side technology. These tools are very interesting and suitable for a cloud installation.
In this article we will talk about KeePassXC, a simple multi-platform open source software that uses a local file as a database.
The main advantage of this type of password management is simplicity. No server-side technology expertise is required and can therefore be used by any type of user.
Introducing KeePassXC
KeePassXC is an open source cross platform password manager: its development started as a fork of KeePassX, a good product but with a not very active development. It saves the secrets in an encrypted database with AES algorithm using 256 bit key, this makes it reasonably safe to save the database in a cloud drive storage such as pCloud or Dropbox.
In addition to the passwords, KeePassXC allows you to save various information and attachments in the encrypted wallet. It also has a valid password generator that helps the user to correctly manage his credentials.
Installation
The program is available both in the standard Fedora repository and in the Flathub repository. Unfortunately the integration with the browser does not work with the application running in the sandbox, so I suggest to install the program via dnf:
sudo dnf install keepassxc
Creating your wallet
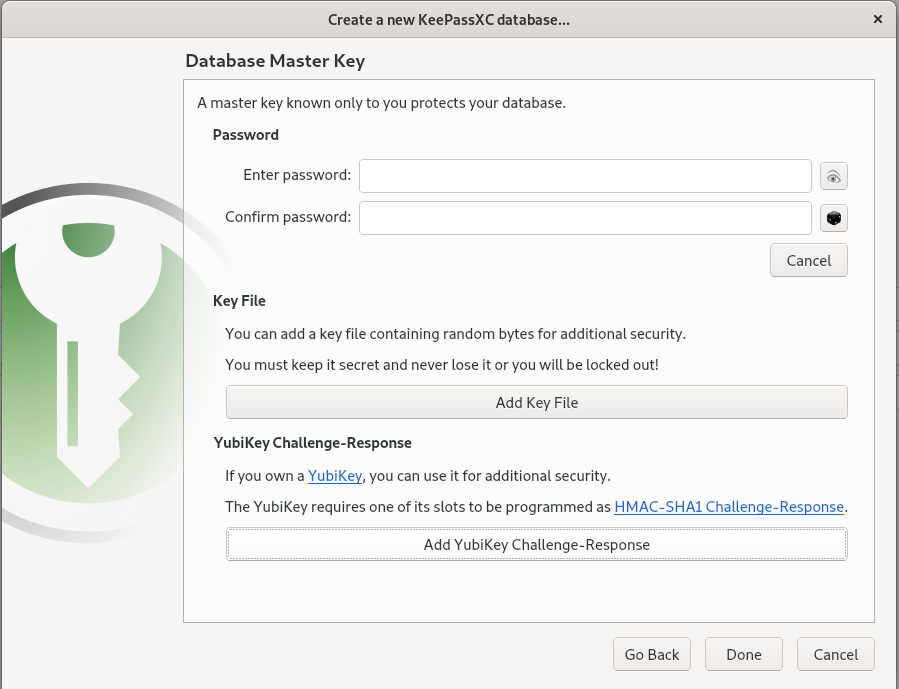
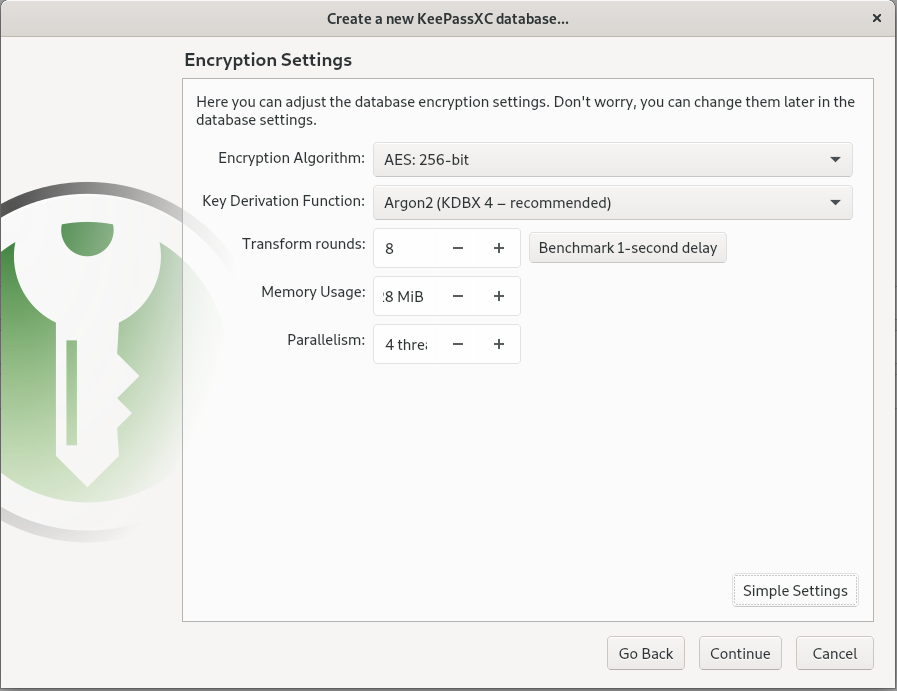
To create a new database there are two important steps:
- Choose the encryption settings: the default settings are reasonably safe, increasing the transform rounds also increases the decryption time.
- Choose the master key and additional protections: the master key must be easy to remember (if you lose it your wallet is lost!) but strong enough, a passphrase with at least 4 random words can be a good choice. As additional protection you can choose a key file (remember: you must always have it available otherwise you cannot open the wallet) and / or a YubiKey hardware key.
The database file will be saved to the file system. If you want to share with other computers / devices you can save it on a USB key or in a cloud storage like pCloud or Dropbox. Of course, if you choose a cloud storage, a particularly strong master password is recommended, better if accompanied by additional protection.
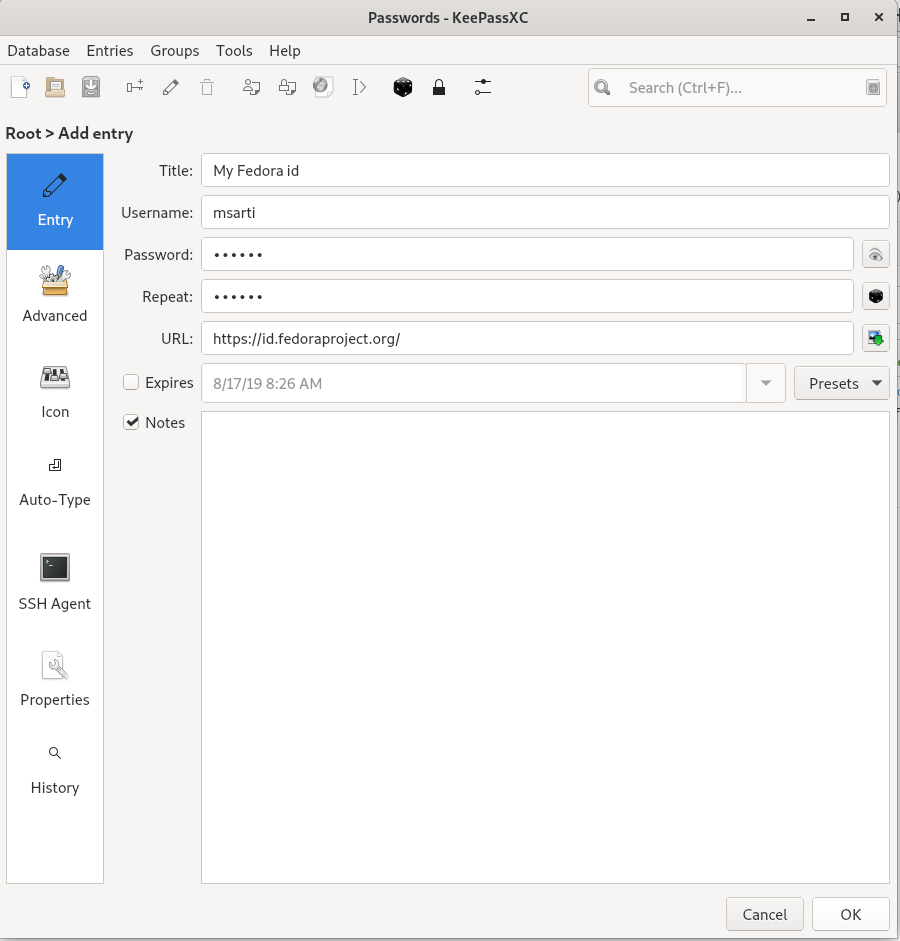
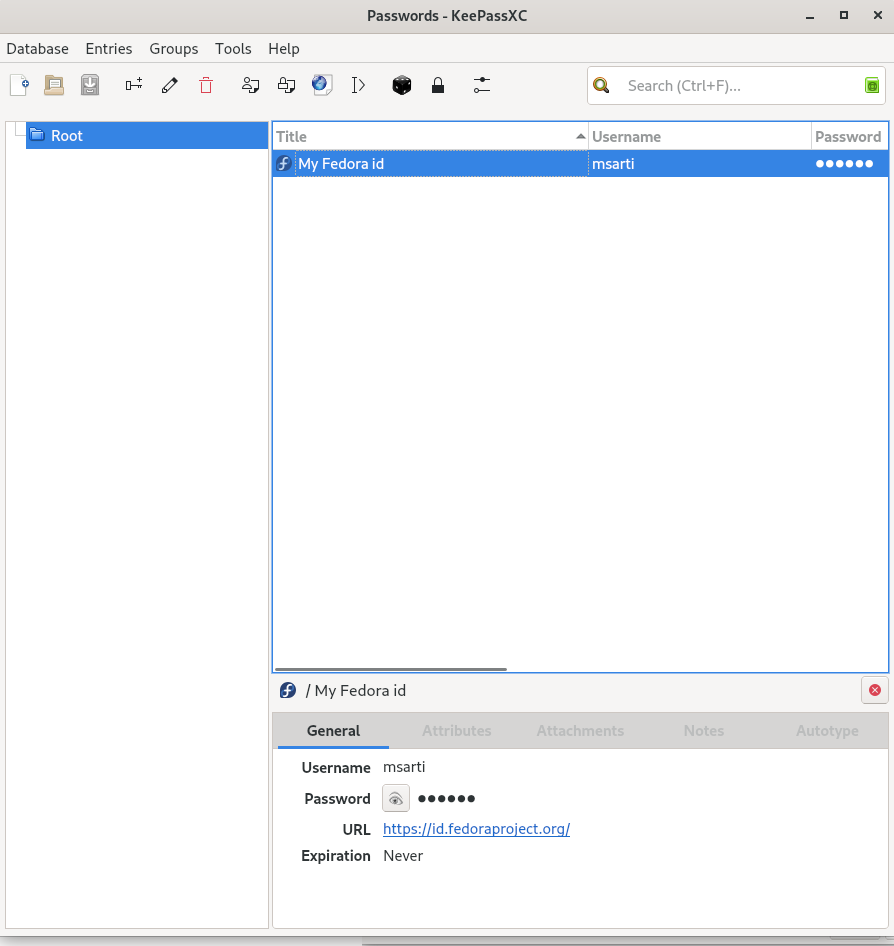
Creating your first entry
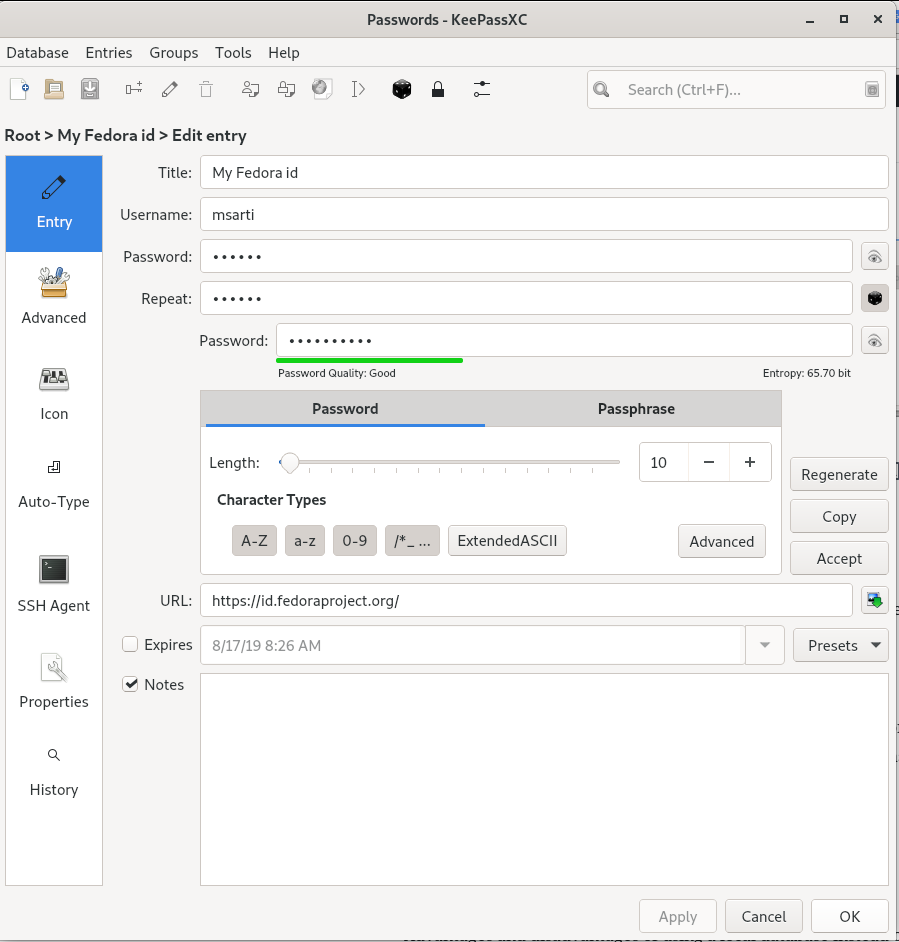
Once the database has been created, you can start creating your first entry. For a web login specify a username, password and url in the Entry tab. Optionally you can specify an expiration date for the credentials based on your personal policy: also by pressing the button on the right the favicon of the site is downloaded and associated as an icon of the entry, this is a nice feature.
KeePassXC also offers a good password / passphrase generator, you can choose length and complexity and check the degree of resistance to a brute force attack:
Browser integration
KeePassXC has an extension available for all major browsers. The extension allows you to fill in the login information for all the entries whose URL is specified.
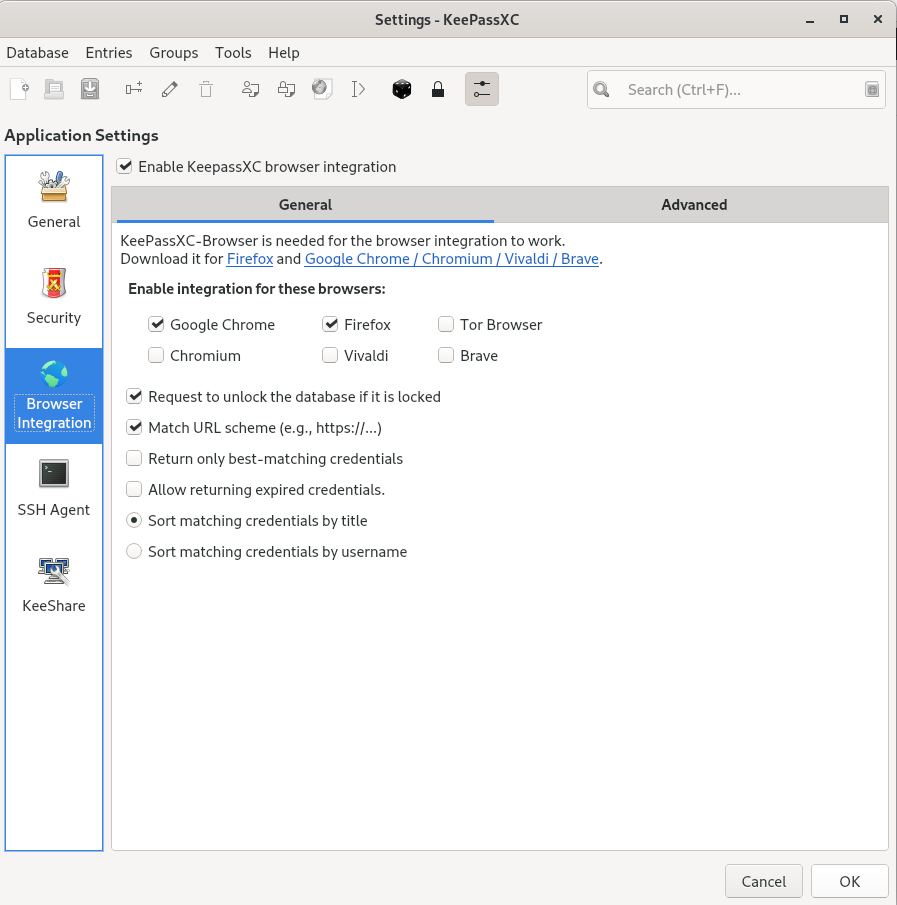
Browser integration must be enabled on KeePassXC (Tools menu -> Settings) specifying which browsers you intend to use:
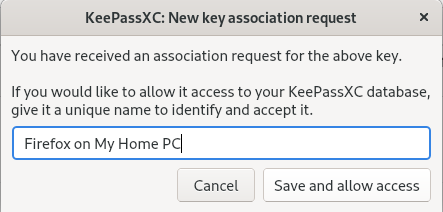
Once the extension is installed, it is necessary to create a connection with the database. To do this, press the extension button and then the Connect button: if the database is open and unlocked the extension will create an association key and save it in the database, the key is unique to the browser so I suggest naming it appropriately :
When you reach the login page specified in the Url field and the database is unlocked, the extension will offer you all the credentials you have associated with that page:
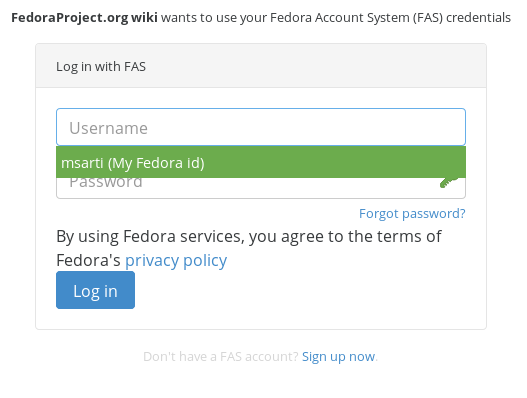
In this way, browsing with KeePassXC running you will have your internet credentials available without necessarily saving them in the browser.
SSH agent integration
Another interesting feature of KeePassXC is the integration with SSH. If you have ssh-agent running KeePassXC is able to interact and add the ssh keys that you have uploaded as attachments to your entries.
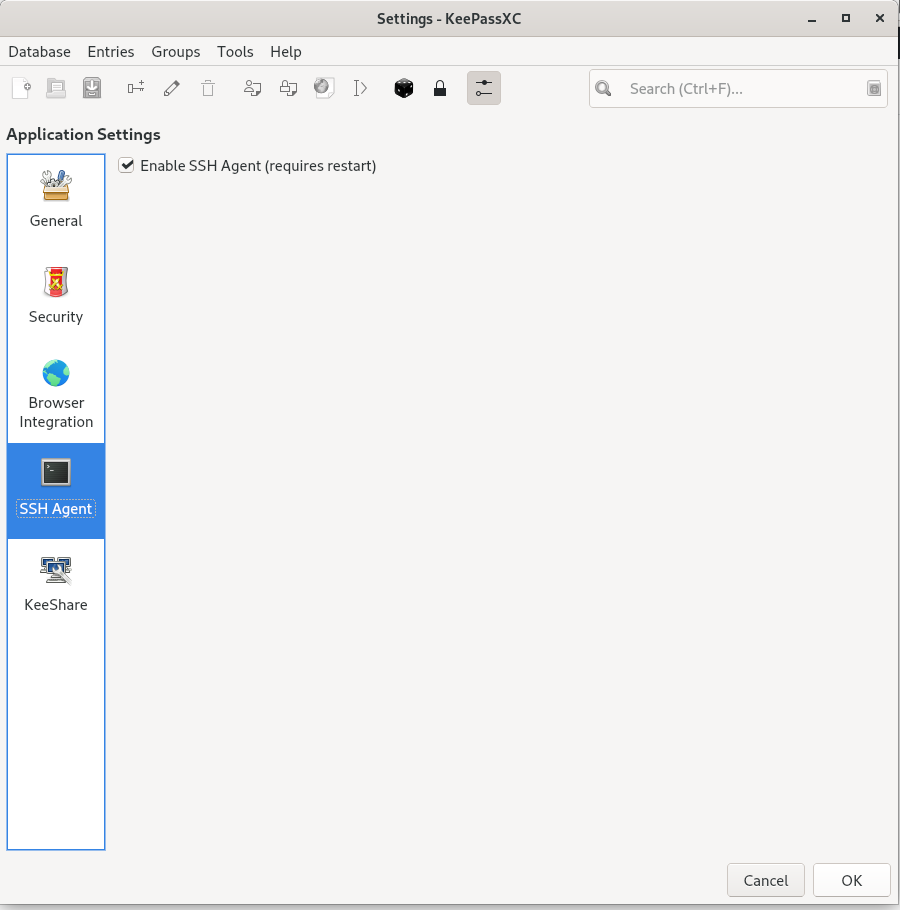
First of all in the general settings (Tools menu -> Settings) you have to enable the ssh agent and restart the program:
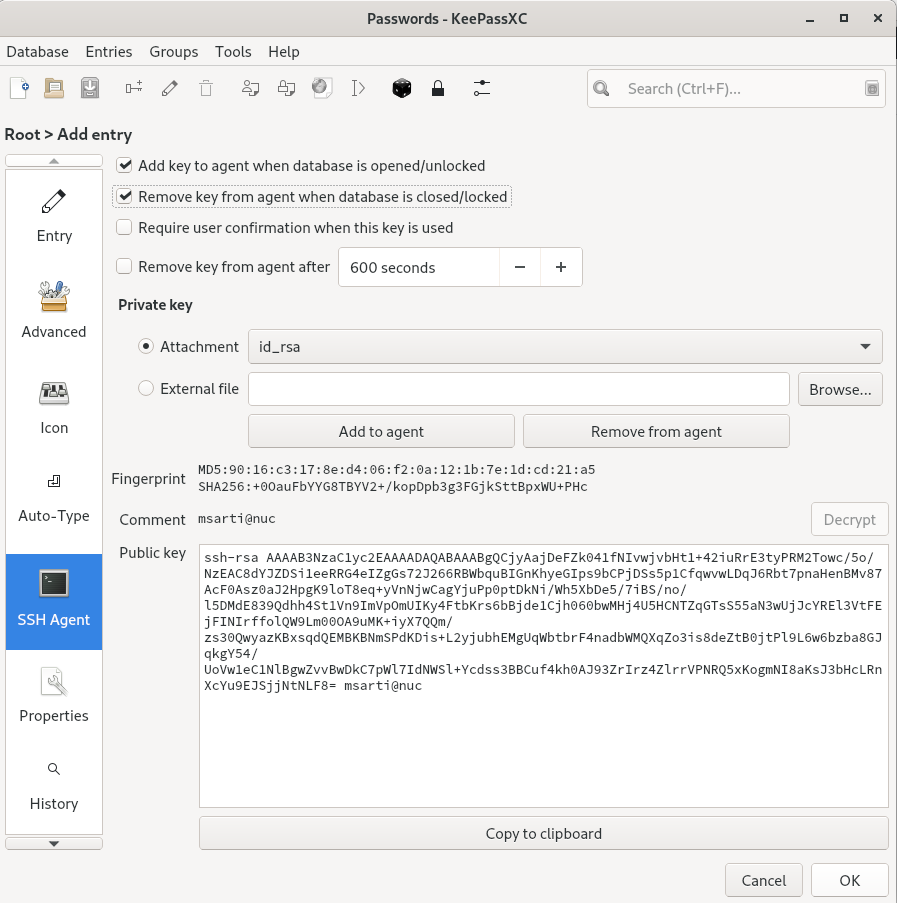
At this point it is required to upload your ssh key pair as an attachment to your entry. Then in the “SSH agent” tab select the private key in the attachment drop-down list, the public key will be populated automatically. Don’t forget to select the two checkboxes above to allow the key to be added to the agent when the database is opened / unlocked and removed when the database is closed / locked:
Now with the database open and unlocked you can log in ssh using the keys saved in your wallet.
The only limitation is in the maximum number of keys that can be added to the agent: ssh servers do not accept by default more than 5 login attempts, for security reasons it is not recommended to increase this value.



Milos
In your ssh config, you can specify a public key for the IdentityFile option instead of the private key.
If you have tons of keys in your agent, that gets around the 5 key limitation as specifying the public key works quite well with the agent.
Try it with ssh -vv. It will be the first key tried.
Johannes
Exactly. I think you could also add
Hosts *
IdentitiesOnly yes
to your ~/.ssh/config file to work around the maximum keys limitation
Patrick
Thanks for this article. Typo: Ubikey -> Yubikey
Besides a Yubikey you can also use a Nitrokey.
Clément Verna
Thanks I fixed the typo 🙂
Joshua
KeePassXC challenge-response will also support the OnlyKey in version 2.5, which gives you reliable (not time based) MFA for your password database.
Walter
A bit offtopic, but anyway…
I have about 100 logins/passwords saved in Firefox and am not willing to re-enter them into the keepassxc-database.
Is it possible to import them right from key4.db file ?
I failed to export the passwords from Firefox with pw-exporter or the like.
hammerhead corvette
There is a “Password Exporter” for Firefox versions 58+(Quantum) to which you can export to CSV & JSON formats. KeepassXC allows for import to CSV.
John
You could export passwords in CSV, then import it back in Keepass, I used https://github.com/kspearrin/ff-password-exporter but I’m sure there are other alternatives 🙂
G. Fernandes
I don’t know how Firefox stores it’s password database, but you’d need some way to export the encrypted (I’m assuming it must be, or there wouldn’t be much point!) database as XML data or CSV.
I’ve done this for transferring data from Revelation to KeePassXC, with a simple Java program (https://github.com/g5-f8s/f8s.java.utils/blob/master/src/main/java/org/g5/pwdmgr/converter/RevelationToKeePassConverter.java).
There is a password plugin that will export passwords stored in Firefox (https://www.intowindows.com/3-ways-to-backup-passwords-saved-in-firefox-57-58/).
Walter
Thanks for all your answers!
But you are referring to the exact tool that didn’t work for me -> passwort-exporter.
I tried it some weeks ago hence I can’t remember the correct error message. But it was something like “wrong master password” .
Spurdo
Can you recommend an iPhone app to read keepassxc containers?
Max
You might try these:
Minikeepass: https://apps.apple.com/us/app/minikeepass/id451661808
KeePass Touch https://apps.apple.com/us/app/keepass-touch/id966759076
I tried one of them, but you should really have a go for yourself to see if it fulfil your needs.
Sincerely
Max
Max
Also Strongbox and keepassium seems nice. will actually try out Keepassium after reading the reddit stream: https://www.reddit.com/r/KeePass/comments/cl35es/in_your_opinion_which_is_the_better_ios_client/
Strongbox: https://strongboxsafe.com/
and
Keepassium: https://keepassium.com/
hammerhead corvette
KeePassXC has been a blessing for me. I came over to Linux some years ago with a password file in a crypt of my own making (Lol). The Auto Type feature is good, and i typically save my db’s to Mega and sync them across several devices. All you have to do is close you db, mount the new one and you are good to go ! The browser implementation is great. Some sites require me to occasionally Redetect login fields but that is one click away.
MX
Sorry, this is compatible with the .kdbx file.
https://play.google.com/store/apps/details?id=keepass2android.keepass2android&hl=en
and
https://centos.pkgs.org/7/epel-x86_64/keepassx2-2.0.3-2.el7.x86_64.rpm.html
Nathan D
I was using Keepassx and Keepassxc for years. I just switched to Buttercup.pw to try it out.
It’s worth a check for anyone interested in a password management tool. You can import from Keepassx without issues too.
Max
I believe that with KeePassXC you have a more flexible design of your security level. Having the database in an airgapped vm, a file in your dropbox for your phone, mac, Linux, windows needs, etc.
It’s all about choice. And maybe KeePassXC wil come for iPhone one day. that’s the only thing needed.
I decided to use, for password manager, the test repository, because I’d rather have the app not working, instead of having a security issue. But that’s just me 🙂
https://www.militant.dk/2019/06/10/keepassxc-2-4-2-on-fedora-30/
Sincerely
Max
Serge Meeuwsen
Nice overview and I would love to migrate back to keepassXC and use the YubiKey; The only thing holding me back is the fact that there doesn’t seem to be an Android / iOS version of keepassXC supporting the Yubikey as well…
Krzysztof
What’s the advantage of using KeePass over saving passwords in Firefox? Firefox password just works on any device set up with Firefox Sync. For KeyPass I have to set it up on all devices (including Dropbox for storing the password database file)
FOOBAZ
I second this, plus Firefox Lockwise works great on my android phone, I can unlock and autofill passwords in different apps using its fingerprint sensor.
tuxflo
The main advantage is, that you can also use Keepass for storing non browser related credentials like the mentioned ssh keys or even credit card Pin numbers. Or for example login combinations for remote connections (RDP) or virtual machines.
Also it is possible to store entire documents or files as attachments (like a scanned copy of your ID) inside the Keepass database.
Kuba
It supporting webdav or nextcloud sync?
zuser
Yes, I have been using for several years keeping database on my personal nc server. Syncs nicely to all computers in the house and android app on mobile devices.